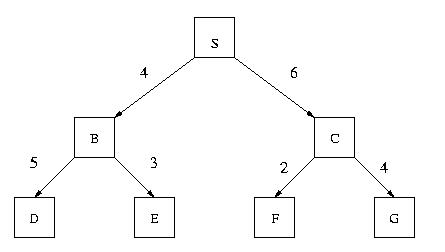
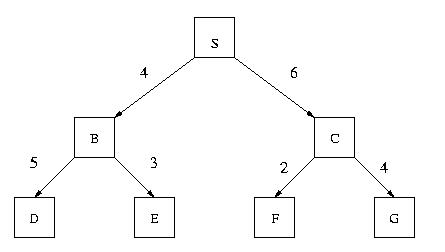
Assume also that the ESTIMATED distances to the goal are given by the following table:
| Node: | S | B | C | D | E | F | G | |||||||
| Estimated Distance to G: | 6 | 1 | 3 | 2 | 5 | 4 | 0 |
For EACH of the following search methods list the nodes in the order in which they are EXPANDED by the search method while looking for a solution. As an illustration, the solution for Depth 1st search is provided below.
List: [S, B, D, E, C, F, G]
List: [S, B, C, D, E, F, G]
List:
[S, B, C]
An alternative answer would be [S, B, D, E, C, F, G] if you use the
convention that depth-limited search expands nodes that are in the
"depth-limit level".
List for depth-limit = 0: []
List for depth-limit = 1: [S]
List for depth-limit = 2: [S, B, C]
List for depth-limit = 3: [S, B, D, E, C, F, G]
An alternative answer would be the one below if you use the convention that depth-limited search expands nodes that are in the "depth-limit level".
List for depth-limit = 0: [S]
List for depth-limit = 1: [S, B, C]
List for depth-limit = 2: [S, B, D, E, C, F, G]
List for depth-limit = 3: [S, B, D, E, C, F, G]
List: [S, B, C, E, F, D, G]
List: [S, B, D, C, G]
List: [S, B, C, G]
List:
List: [S, B, C, D, G]
 You select the second child of the root node as your next move since
that child produces the highest gain.
You select the second child of the root node as your next move since
that child produces the highest gain.
Nodes marked with an "X" are not evaluated when alpha-beta pruning is used. None of the nodes in the subtree rooted at the node marked with an "X" in the third level of the tree are evaluated.
Assume that the operator ">=" (greater than or equal) is a basic operator
implemented in the inference engine.
The working memory contains the following assertions:
Bill can vote
| (Using R4)
|
Bill is an American
/ (Using R1) \ (Using R2)
/ \
Bill was born in the US Bill receives US citizenship
| (succeeds!)
| WM <- {Bill is an American.} Fails!
Bill is an adult
| (Using R3)
|
Bill's age >= 18
Fails!
So, Bill cannot vote!
Using R1
| ?x was born in the US
|
Bill was born in the US
Succeeds!
WM <- { Bill is an American.}
Using R2
| ?x received US citizenship
|
Sue received US citizenship
Succeeds!
WM <- { Sue is an American.}
Using R3
| ?x's age >= 18
|
Sue's age >= 18
Succeeds!
WM <- { Sue is an adult.}
Using R4
/\ ?x is an American
/ \
/ \
Bill is an American. Sue is an American
| ?x is an adult | ?x is an adult
| |
Bill is an adult Sue is an Adult
Fails! Succeeds!
WM <- { Sue can vote.}
COMPUTER USERS
/ |
/ |
ako/ | ako
/ |
/ |
UNIX USERS PC USERS MICROSOFT
CUSTOMERS
\ / \ /
\ / \ /
ako\ /ako ako\ /ako
\ / \ /
\ / \ /
LINUX USERS WINDOWS98
USERS
\ /
\ /
is-a \ /is-a
\ /
\ /
AMY
|
|
|
| Amy | Amy-Linux Users, Linux Users-Windows98 Users |
| Linux Users | Linux Users-Unix Users, Unix Users-PC Users |
| Windows98 Users | Windows98 Users-PC Users, PC Users-Microsoft Customers |
| Unix Users | Unix Users-Computer Users |
| PC Users | PC Users-Computer Users |
Class Precedence list :
Amy
Linux Users
Unix Users - Use C
Windows98 Users
PC Users - Use C++
Computer Users - Use Fortran
Microsoft Customers
What is the value obtained for Amy's favorite programming language according to the class-precedence list you constructed above? Explain you answer.
Amy's favorite programming language is C